In 2018, it’s time to get off the floor, stop yawning, stop ignoring the open bowl on the floor and get serious about your passwords. At least it is for me. Don’t be stuffing my creds!
As supposedly a technologist, I’ve been putting this off way too long.
Warning lights flicked on for me earlier this month. Driving across Montana I was listening to an episode of Reply All about The Russian Passenger.
Without going too deep into it, the people on the show work through a situation where radio personality Alex Blumberg returned home from a trip out of the country. He was surprised, then alarmed, to find charges on his Uber account was being used for someone else… getting rides in Russia. A rabbit hole adventure winds through the door when Uber reports there is for account associated with his card number, despite the fact that he had just been billed.
The story winds through alleys of possible Gmail hacks, a Windows surface possible hack, an Uber breach that did not account for a lost password. Coming from a news show, it’s apparent they have access to talk to top security people at companies we would never have as individuals. Even with that, the real cause of how Alex’s credentials were hijacked are still left to conjecture.
The gist, at least for me, is an awakening that the real problem is a lazy practice of using the same password on different web sites. If anything, the recent flood of GDPR driven privacy policy change notices is a reminder of the potential impact when we use email addresses and the same passwords even on sites we rarely use or have forgotten about.
Positive things about getting all these privacy policy update notices? Finding out which crappy old web services accounts I can now delete.
Negative things? Finding out that some services, I have to make a frigging phone call to delete an account
— Alan Levine (@cogdog) May 21, 2018
Password hacks are hardly news; it happens all the time. We dutifully get notified and update passwords… to something we can easily remember. B
But the problem is hardly where the hack/breach occurs, more so that it puts out there a password you used on one site you barely remember signing up for, and then using the same password elsewhere… and that a common thing on web sites is using your email as a user name.
So companies’ websites are hacked every single day. Last year we had LinkedIn, Myspace, VK.com. All of these other breaches of tens if not hundreds of millions of accounts. Uh, with email addresses, and passwords being traded amongst hackers. But if you’re a clever hacker, you’re not only going to use those details, to break into accounts on that one site, you’re gonna see if they work on something else. The problem there is that people are using the same password on multiple websites and services.
All they’re doing is reusing the password, but they’ll have a special piece of software which can just churn through just hundreds if not thousands, very very quickly. The more that me and my colleagues report on these data breaches every other day, every week, it is password reuse that is the main threat to ordinary users of the internet for sure.
This is credential stuffing. Your passwords and linked to email addresses, are made available through breaches of companies you have trusted them too (well with Equifax, they just do pile up data without you asking), and are shopped around in weird virtual malls you never would venture to go, the dark web.
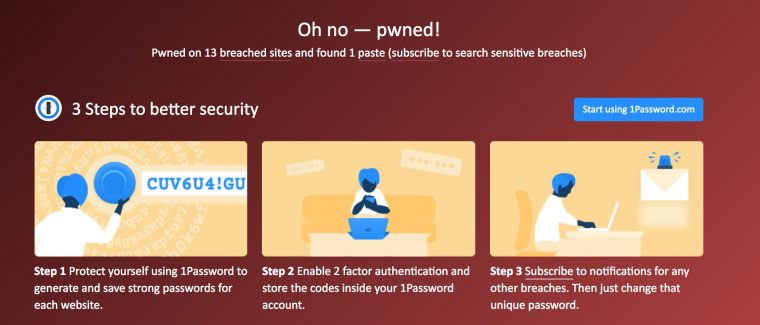
If you really want to get jolted, pop your email into https://haveibeenpwned.com/.
This is what got my attention:
My listings included possible leaking of my password from breaches at Adobe, bit.ly, kickstarter, dailymotion, last.fm (where I have an account I never recall using)… Maybe it’s time to try Deseat.me but then again, people question whether its wise to again toss your email address out there? All it is doing is scanning your email for account creation/unsubscribe info. Heck, I can search my email myself.
Donning a tinfoil hat, I pass.
And so while I changed passwords when warned by those sites listed above, did I check to see if I used the same combos elsewhere?
Hmmm, that seems hard to remember. But its something people doing credential stuffing can figure out by sheer brute computing force. That steam engine stumps my human powered brain.
Now I do have a system I’ve used for passwords; I don’t reuse one single password all over the place, but I have a means of combining key words only I know. When I have a reminder for a site, I might have codes like 5F or 3Y or B9 (those are not the real ones) all that represent unique words I know. I sometimes do a thing where I delete 1 letter if the sites name has an odd number of characters in the URL and 2 if its even. But my system is hardly consistent.
But even that means I have a lot of sites using the same passwords, even if they are obscure. And could they withstand brute force attempts to remix them? It’s not the passwords themselves that are the problem; it’s that you should never use the same password on more than one site.
No one can remember that, so thus password managers are the optimal approach, with the exception there is a single point of entry, so make sure that password is very unique/memorable/not stored where someone can find it. I cannot recommend one being better than others (see links)
This is something that I have been ignoring for too long. I do use a password mamager, and I have created strong, unmemorable ones for bank accounts, gmail, etc. But I have a lot more that were not unique and crazy long.
Until tonight.
I started going through my major accounts and setting unique, crazy long passwords I cannot remember. Turning on 2 factor authentication where I can.
This stuff is hardly new, I’ve just been cat napping too long with an open password bowl.
The inconvenience of non-memorable passwords is worth taking on as opposed to finding out your credit card is being used for paying for Uber rides in Russia that are not your own. Listen to this Reply All podcast if you need some more incentives.
If you have been putting this off, stop. If you are going to put anything on a yellow sticky, don’t make it your password, make it a note that says:
Featured Image: Lazy Cat flickr photo by Mark Turnauckas shared under a Creative Commons (BY) license modified to include Password hacking illustration Wikimedia Commons image by Santeri Viinamäki shared under a Creative Commons CC BY-SA license.
If I do my CC math correctly, the composite image should be licensed Creative Commons CC BY-SA license (? my head hurts)